| 30% of breaches involve insiders or compromised accounts |
280 days avg. time to identify a breach without behavioral analytics |
60% reduction in false positives with AI-tuned UEBA |
$4.45M average cost of a data breach (IBM 2025) |
The Limits of Perimeter Defense
Firewalls, VPNs, and signature-based antivirus were built for a network era that no longer exists. Cloud-first architectures, remote workforces, and SaaS sprawl have dissolved the clean perimeter those tools relied on.
Perimeter tools can’t see inside
Once a threat actor is inside via stolen credentials or a compromised device legacy tools are essentially blind.
Detection lag is catastrophic
Attackers dwell an average of 9+ months before detection in environments without behavioral analytics.
Rule fatigue is real
Static SIEM rules require constant manual updates and still generate thousands of low-quality alerts daily.
What UEBA Actually Does
UEBA — User and Entity Behavior Analytics extends traditional log analysis by profiling the behavior of every actor in your environment: users, devices, service accounts, and applications.
| Traditional UBA | Modern UEBA |
|---|---|
| Focuses only on user accounts | Users + devices + apps + services |
| Static rule thresholds | Dynamic behavioral baselines |
| Minimal context enrichment | Peer group + time context |
| High false positive rate | Risk-scored, prioritized alerts |
UEBA doesn’t ask ‘does this match a rule?’ – it asks ‘does this match what this entity normally does?’
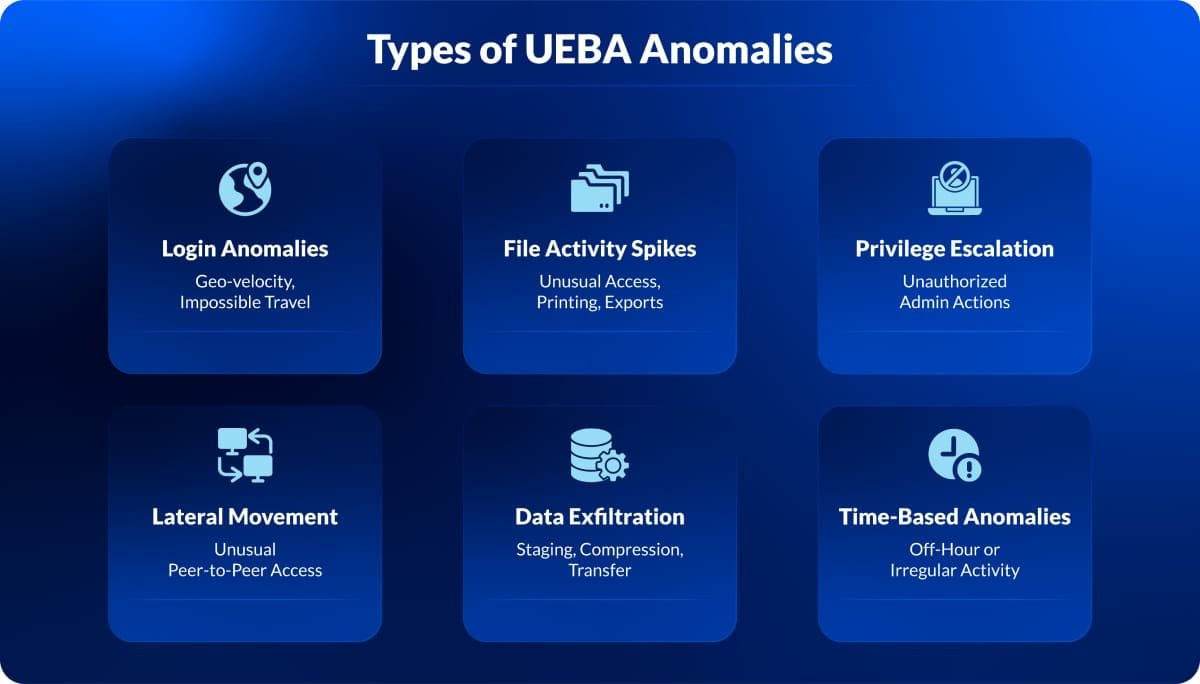
Anomalies detected by UEBA
UEBA identifies unusual patterns of behavior that fall outside normal activity. Rather than relying on static rules, it builds behavioral baselines and highlights deviations that may signal a security risk.
These anomalies can occur across logins, file access, permissions, or user activity timing. While a single event may not indicate a threat, multiple anomalies occurring together often point to suspicious or malicious behavior.
This approach allows security teams to detect threats earlier and focus on high-risk activity instead of noise.
Where AI Changes the Game
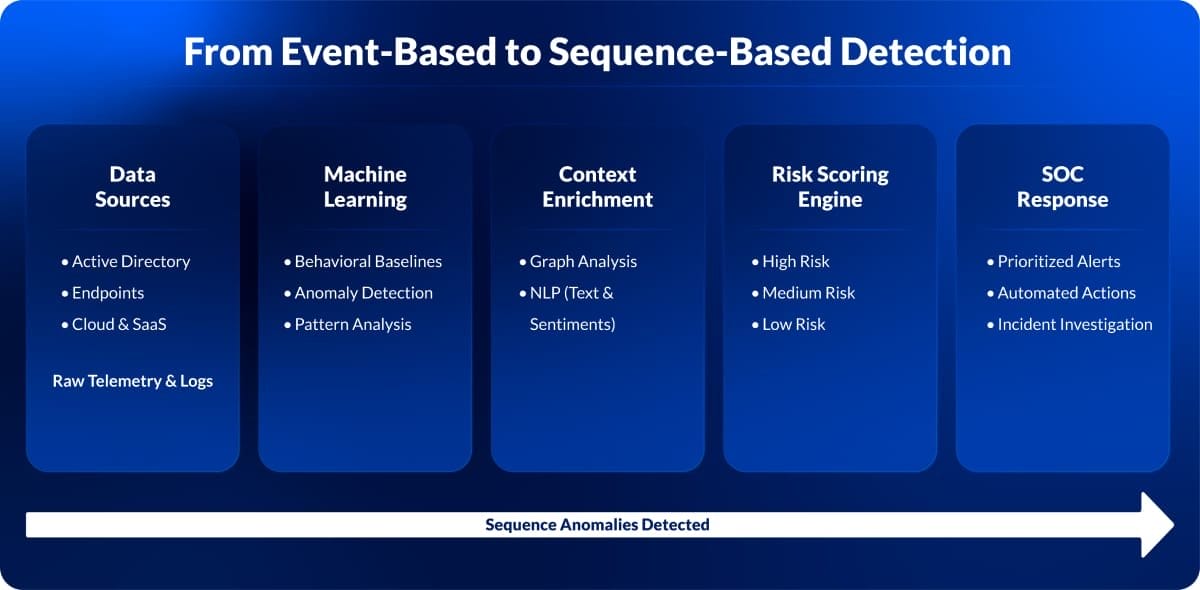
Rule-based UEBA can detect known attack signatures. AI-driven UEBA detects unknown ones by learning what normal looks like across millions of events per day.
Machine Learning
Models continuously retrain on fresh data, profiling a new employee within days without manual configuration.
NLP + Graph
Correlates email content, chat logs, and file metadata to understand intent, not just raw log events.
Deep Learning
LSTM and transformer models detect multi-step attack chains that no single event would trigger as an alert.
Risk Scoring
Prioritized alert queues. Instead of 500 equal-priority alerts, AI surfaces the 5 that represent genuine risk with confidence scores.
Key Use Cases in Enterprise Security
Credential Misuse and Account Takeover
A valid login from an unfamiliar country combined with unusual access patterns triggers a high-risk alert even if the password is correct. AI detects context-level anomalies that static IP blocking cannot.
Insider Data Exfiltration
An employee downloads 3x their weekly average of sensitive documents, compresses them, and moves files to an unmanaged USB all within a 20-minute window. Behavioral deviation, not content scanning, catches this.
Privilege Escalation and Admin Abuse
A service account making Active Directory changes it has never made before flags as anomalous, even if it technically has permission. UEBA models ‘normal use of permissions,’ not just ‘has permission.’
Lateral Movement Detection
After an initial compromise, attackers move laterally to find crown jewels. AI-powered graph analysis maps unusual peer-to-peer connections across the network invisible in raw logs.
IoT and Non-Human Entity Monitoring
Industrial devices, printers, and HVAC systems now have network access. UEBA extends behavioral profiling to non-human entities flagging a medical device scanning internal IP ranges, for example.
Platform Comparison: Leading UEBA Solutions
Below is a comparison of leading UEBA solutions:
| Platform | AI Approach | Native SIEM Integration | Cloud-Native | Best Fit |
|---|---|---|---|---|
| Microsoft
Sentinel UEBA |
ML + Graph Analytics
(Azure) |
✓ | ✓ | Microsoft-heavy
enterprises |
| Splunk UBA | Unsupervised ML,
Clustering |
✓ (Splunk ES) | ✓ (Hybrid) | Large SOCs with existing
Splunk |
| Exabeam Fusion | Smart Timelines + Risk
Scoring |
✓ (Built-in) | ✓ | UEBA-first deployments |
| Securonix | NLP + Behavioral
Threat Models |
✓ | ✓ | Regulated industries
(Finance, Healthcare) |
| IBM QRadar
UEBA |
ML + Peer Group
Analysis |
✓ (QRadar) | ✗ (On-prem
focus) |
Government & critical
infrastructure |
Challenges You Can’t Ignore
Data Quality
UEBA is only as good as the logs it ingests. Inconsistent timestamps, gaps in coverage, or siloed data sources create blind spots that attackers exploit.
Skill Gap
AI surfaces anomalies and analysts must interpret them. Without trained SOC staff, even a well-tuned UEBA deployment generates noise rather than signal.
Privacy and Compliance
GDPR, CCPA, and labor laws constrain what behavioral data can be collected and retained. Legal and HR must be in the loop before deployment.
Baseline Time
New deployments need 2–4 weeks of baseline learning before generating reliable anomaly scores — during which visibility is limited.
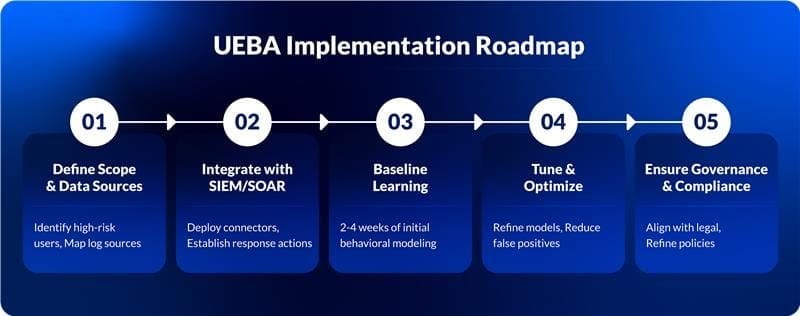
Implementation Roadmap
A phased approach reduces deployment risk and gets value to the SOC faster.
01 – Define scope and data sources
Identify high-risk populations (privileged users, contractors, finance team) and map log sources: AD, endpoint EDR, cloud access logs, DLP.
02 – Integrate with existing SIEM/SOAR
Map alert outputs to SOAR playbooks to enable automated triage for lower-risk findings.
03 – Establish behavioral baselines
Allow 2–4 weeks of passive learning. Avoid acting on raw anomaly scores during this window.
04 – Tune risk thresholds
Calibrate sensitivity with SOC analysts. Benchmark against known-good and known-bad events.
05 – Enable cross-team governance
Establish a UEBA committee including IT, Security, Legal, HR, and Compliance. Define escalation paths and data retention policies.
06 – Continuous model maintenance
Retrain models quarterly. Review false positive rates monthly. Update peer group definitions as the org structure evolves.
Real-World Detection Scenarios
Financial Services – Insider Trading Prevention
A regional bank’s UEBA platform flagged a compliance analyst who accessed merger documentation outside business hours, then emailed a personal account. Investigation confirmed unauthorized information sharing. Detection latency: 4 hours.
Healthcare – Patient Record Snooping
A hospital deployed UEBA across its EHR system and caught a nurse accessing 200+ patient records outside her assigned unit; a HIPAA-reportable violation that legacy access logs had missed for 6 months.
Manufacturing – IP Theft at Departure
In the two weeks before a senior engineer resigned, UEBA detected a 900% spike in CAD file access and USB transfers. The security team intervened before the employee left with trade secrets.
The Future: AI-Driven Security Ecosystems
Convergence with XDR
UEBA is merging into Extended Detection and Response platforms, giving behavioral analytics access to endpoint, network, cloud, and email telemetry in a single correlated view.
Predictive threat intelligence
Next-gen UEBA will surface behavioral precursors to exfiltration that appear days before the actual event.
Autonomous SOC first response
AI agents will handle Level 1 triage autonomously, enriching alerts, correlating context, isolating endpoints, and escalating only cases requiring human judgment.
LLM-powered investigation assist
Analysts will query their UEBA platform in natural language: ‘Show me all privileged accounts that accessed finance systems within 24 hours of a failed login attempt last quarter.’
Attackers Already Know Where You’re Blind
AI + UEBA is the one that shifts focus from perimeter hardening to understanding behavior: what normal looks like, what deviation means, and how fast you can respond when something breaks the pattern.
Modern threats don’t trigger obvious alerts.They hide in normal-looking behavior.
If your detection relies on rules, you’re already behind. UEBA shifts the focus to what actually matters: deviations, patterns, and intent.
Check:
Are you detecting threats or just reviewing alerts?
If it’s the latter, it’s time to rethink your detection approach with AI + UEBA.
Schedule a UEBA readiness assessment
Identify gaps in visibility, data quality, and behavioral coverage before attackers do.