The Illusion of DLP Readiness
Walk into most enterprises today and ask a simple question, “Are you audit-ready from a data protection standpoint?” and the answer is almost always yes.
Policies exist, tools are deployed, and reports can be generated on demand. On the surface, everything appears under control. But beneath that surface lies a different reality.
DLP in many organizations has become a checkbox function. It is implemented to satisfy regulatory expectations rather than to actively reduce risk.
The system flags
- Violations
- generates alerts
- Logs events
But rarely does it provide meaningful insight into how data actually moves, who is interacting with it, or whether that interaction is risky.
This creates a dangerous illusion of visibility without understanding, control without confidence. In 2026, that illusion is beginning to collapse.
Why Compliance is Raising the Bar
Regulatory frameworks are no longer satisfied with static evidence. The shift is subtle but significant. Instead of asking whether controls exist, auditors increasingly want to understand whether those controls are effective in real world conditions.
This means organizations are expected to demonstrate not just that a DLP solution is in place, but that it can detect abnormal data behavior, respond to potential threats in real time, and adapt to changing risk patterns.
The rise of
- Hybrid work,
- SaaS adoption
- AI driven
Workflows have made data movement more dynamic than ever.
Sensitive information flows across endpoints, cloud platforms, and collaboration tools, often outside traditional monitoring boundaries. Compliance standards are evolving in response, demanding continuous visibility and contextual awareness. In this new landscape, a static DLP policy is no longer defensible.
The Shift from Control to Context
What separates effective DLP in 2026 from legacy implementations is not broader coverage, but a deeper understanding.
Traditional DLP systems operate on predefined rules. They look for patterns such as
- Credit card numbers
- Confidential keywords
- Large file transfers
While these signals are useful, they lack context. They cannot distinguish between legitimate business activity and subtle indicators of risk.
Modern DLP, however, is increasingly driven by behavioral intelligence. It asks different questions — Is this user accessing data in a way that deviates from their normal pattern? Is the timing, volume, or destination of data transfer unusual? Does this activity align with the user’s role?
By shifting from static control to contextual analysis, organizations move closer to identifying real threats rather than reacting to generic violations. This is particularly critical for insider risk, where the difference between normal and malicious behavior is often nuanced.
What a Modern DLP Strategy Looks Like
A modern DLP strategy is not defined by a single tool but by how well it integrates into the broader security ecosystem.
It operates across
- endpoints
- Networks
- Cloud environments
Providing consistent visibility regardless of where data resides. More importantly, it aligns with a zero-trust philosophy, where no data movement is inherently trusted, and every interaction is evaluated based on context.
Automation plays a critical role here. Instead of overwhelming security teams with alerts, advanced DLP systems prioritize incidents based on risk, enrich them with contextual information, and enable faster, more informed responses.
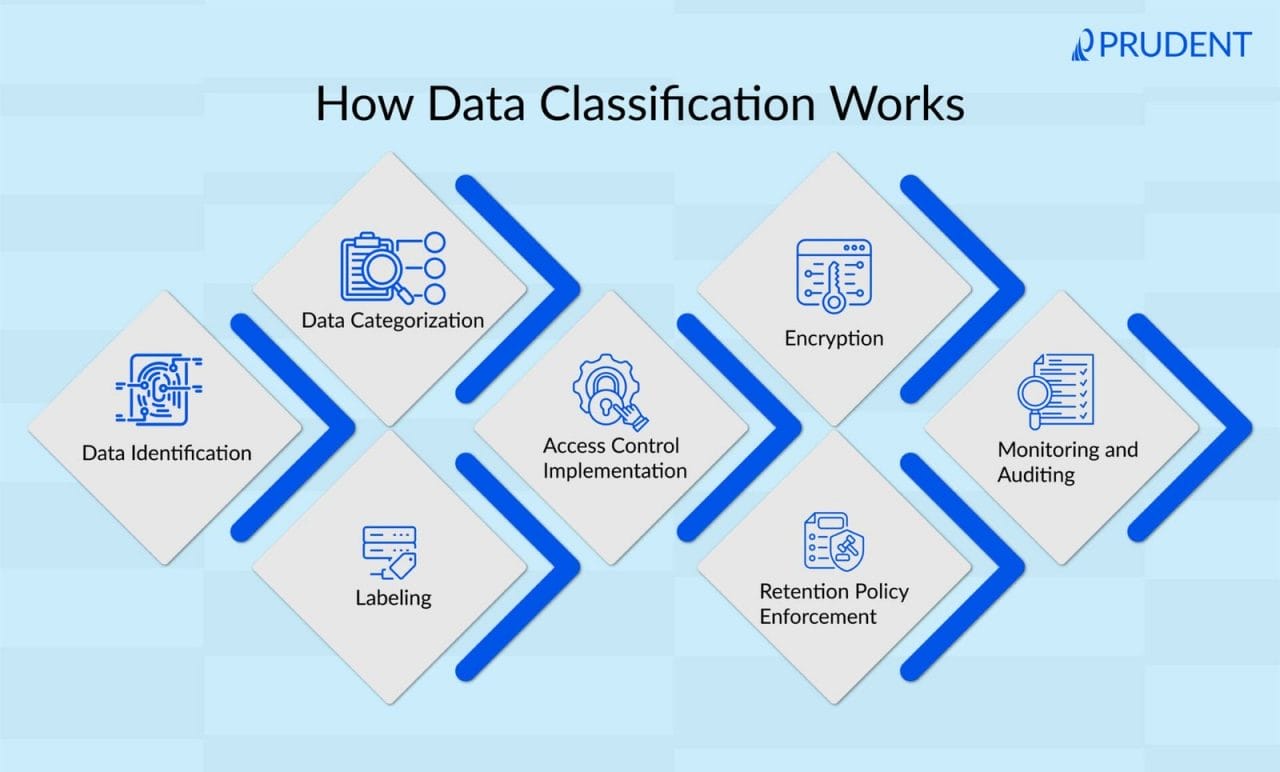
Data classification also evolves beyond manual tagging. Intelligent systems continuously identify and categorize sensitive information, ensuring policies remain relevant even as data changes. The result is a shift from reactive monitoring to proactive risk management.
Selecting the Right DLP: A Leadership Perspective
Choosing a DLP solution in 2026 is no longer a technical decision alone; it is a strategic one. Leaders must look beyond feature checklists and vendor promises.
The real question is whether the solution aligns with how the organization operates today and how it will evolve tomorrow.
This requires evaluating
- How well the platform understands user behavior.
- How effectively it reduce noise.
- How seamlessly it integrates with existing security tools.
It also means considering scalability, especially in environments where data volumes and sources are constantly expanding.
Perhaps most importantly, decision makers must assess whether the solution provides measurable outcomes. Can it demonstrate reduced risk? Can it show improved response times? Can it provide insights that influence business decisions?
A DLP solution that cannot answer these questions will struggle to deliver value—regardless of how advanced it appears on paper.
The Cost of Getting It Wrong
The consequences of ineffective DLP extend far beyond failed audits. Data breaches today are not just technical incidents; they are business crises.
They impact
- Customer trust
- Regulatory standing
- Financial performance
In many cases, the root cause is not a lack of tools but a lack of visibility and understanding.
When DLP fails, it often fails silently. Risks go unnoticed until they materialize into incidents. By then, the cost of remediation far exceeds the investment required to prevent them.
In this context, choosing the wrong solution is not just a missed opportunity; it is a strategic liability.
From Audit Readiness to Risk Readiness
As enterprises approach their next compliance audit, the focus should not be on passing the assessment but on redefining what readiness means.
Audit readiness is temporary. It is achieved at a point in time. Risk readiness, on the other hand, is continuous. It reflects an organization’s ability to understand, monitor, and adapt to evolving threats.
In 2026, the organizations that lead in data protection will not be those with the most policies or the most alerts. They will be the ones with the clearest visibility, the strongest context, and the ability to act before risks escalate.
Enterprise DLP, when implemented correctly, becomes more than a compliance tool. It becomes a strategic enabler, one that not only protects data but also builds trust, resilience, and long-term advantage.
Closing Thought
The next time your organization prepares for a compliance audit, it’s worth asking a different question
Are we proving control, or are we actually in control?
Because in today’s environment — that difference defines everything.